This article takes a deeper look at second layer blockchain scaling off-chain solutions, with various implementations that are progressing as we speak.
The internet was born as an instrument for radical self-expression. When the web was young, it was all about creativity and experimentation in a truly decentralized peer-to-peer fashion. However, over time it grew from a network of hobbyists into a multi-billion industry and gradually its great power was usurped by corporations, governments, and large ISPs. Over three billion people use the internet monthly, although it’s just a handful of ISPs that serve the majority of the traffic in each country. The internet has grown to billions of websites, but most user activity is happening on Facebook, Google, Twitter, and other major platforms.
(Read also: Guide to Open Source: Importance of Open Source Technology in Cryptocurrency)
Blockchain Technology
The creation of Bitcoin in 2008 was a ground-breaking advancement in technology, promising to bring real changes to our world. The elements of decentralization, transparency, and immutability captured the imagination of many and posed a threat to traditional systems. This revolution was similar to that of the internet back in the 1990s, but with much greater intensity.
After almost a decade, the cryptocurrency landscape has evolved into a vibrant and diverse ecosystem with numerous coins and tokens with trying to solve different problems. However, much is still to be done for blockchain technology to be accessible to the mainstream public.
(See also: 3 Major Industries That Blockchain Technology is Changing)
Main Problem: Scalability
The goal of any real blockchain technology is to empower the masses through freedom and true decentralization. Bitcoin is the digital equivalent of money, but unlike traditional fiat money, it is not controlled by any single entity. Another popular manifestation of blockchain technology is Ethereum, which is a blockchain platform that facilitates the creation of decentralized applications (dApps) and tokens.
While very few can undermine the potential of blockchain technology, there are still major hurdles that limit its capabilities. In the pursuit of decentralization and immutability, blockchain technology suffers from scalability and speed issues. This phenomenon has a formal proof and is called the Decentralization, Consensus or Scale (DSC) trilema or DCS Theorem. In order words, a blockchain can achieve only two of the following three properties in a distributed system:
- Decentralization: This addresses the question main questions; ‘To what extent the system is resistant to the failure of its singular element?’ and ‘How much power or influence does an entity possess?’
- Consensus: This refers to whether decisions are made by a consensus of all parties or single-handedly by a small group of users
- Scale: This refers to the capability of a system to cater to a larger user base, without slowing down or compromising the system
A blockchain cannot have all 3 properties; only 2 attributes can be chosen. That is why scalability, speed and throughput is an inherent problem for a public blockchain focused on upholding the principles of decentralization. However, the cryptocurrency community has been hard at work to find solutions that will address the issue of scalability.
(Read more: Top 10 Crypto/Blockchain Infographics You Must Know)
Other Pressing Issues
Another major issue faced by blockchains is privacy. The nature of consensus-driven distributed databases like Bitcoin and Ethereum is that all transaction data is stored on the blockchain and is tamper-proof. This means that all transaction data can be publicly verified and cannot be changed or altered in any way. This is important for achieving decentralization but not necessarily ideal for personal or commercial privacy. Second layer scaling solutions are addressing this issue.
Before diving deep into the analysis of existing solutions, it is worth noting that off-chain scaling is not the only option. For instance, one can achieve good scaling capabilities by sacrificing the decentralization attribute of a blockchain. Such an approach is pioneered by Delegated Proof-of-Stake (DPoS) blockchains, such as Bitshares and EOS. In a DPOS system, the network nominates a few nodes as representatives. This requires a degree of trust since these nodes are responsible for processing transactions in an honest manner.
Public blockchains are pretty much ideal examples of the network effect; high usage of the network attracts more applications, businesses, and users. That is why there won’t be too many base-level (protocol) blockchain platforms in the market; rather, all usage will converge on a few of the most advanced, highly secure and widely used networks. For instance, Bitcoin being used for payments and money while Ethereum is used for dApps and trustless code execution.
(See also: Guide to Blockchain Protocols: Comparison of Major Protocol Coins)
Blockchain Scaling Solutions
There are already several solutions that try to solve the issue of blockchain scalability.
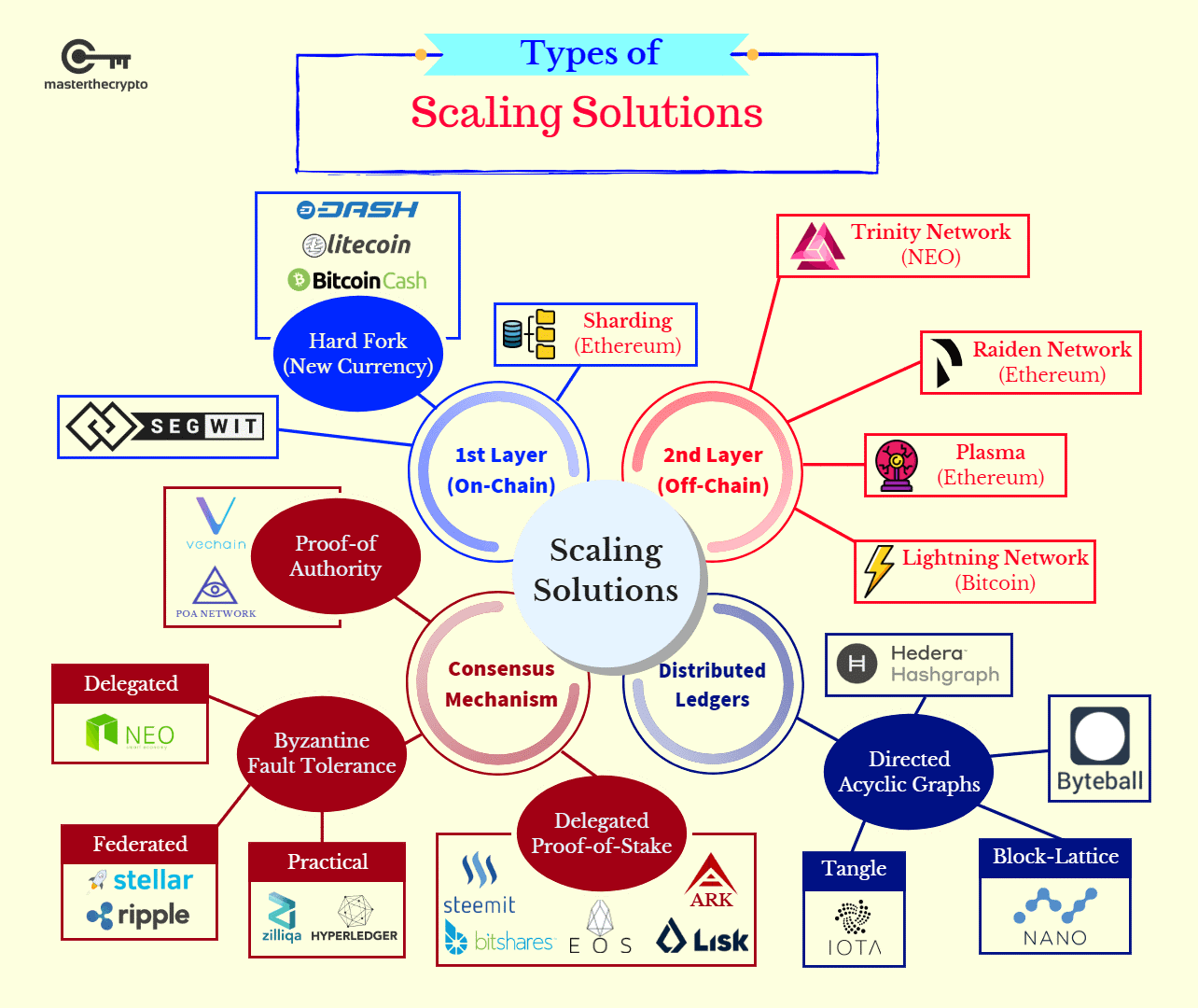
From the classification above, there are 4 categories of scaling solutions that is being explored by the community;
- First Layer (On-Chain) Solutions: Also known as the protocol-layer solution, first-layer solutions require fundamental changes to be made onto the codebase of the actual blockchain (hence the term “on-chain”. This entails engaging in updates such as increasing the block size limit or reducing the block creation time.
- Second Layer (Off-Chain) Solutions: This refers to secondary applications or channels that are built on top of the main blockchain and do not require any fundamental changes to the actual blockchain. The bulk of transactions are ‘off-loaded’ to the secondary channels to reduce network congestion and facilitate faster processing speeds.
- Consensus Mechanisms: Perhaps the most important mechanism of any blockchain, scalable consensus mechanisms streamline the consensus process to allow for greater scalability and transaction processing output.
- Scalable Distributed Ledgers: Another form of distributed systems that have a different data structure compared to a blockchain. Distributed ledgers usually use a linear data structure rather than organizing transaction data into chained, sequential blocks like a blockchain do.
This article would be focused on examining second-layer scaling solutions, which are also called off-chain scaling solutions.
Classification of Layer 2 Solutions
Sidechains were one of the first proposals on achieving unlimited scaling and preserving privacy while maintaining the security of the base-layer protocol. Sidechains allow users to lock some coins up on the main chain and in return get coins on the parallel chain with its own rules, consensus and much more flexibility on how the protocol is governed. Sidechains add throughput, flexibility and allow one to experiment with consensus rules. Some implementations of sidechains that are close to ready include Liquid and Rootstock sidechains for Bitcoin, and Plasma for Ethereum.
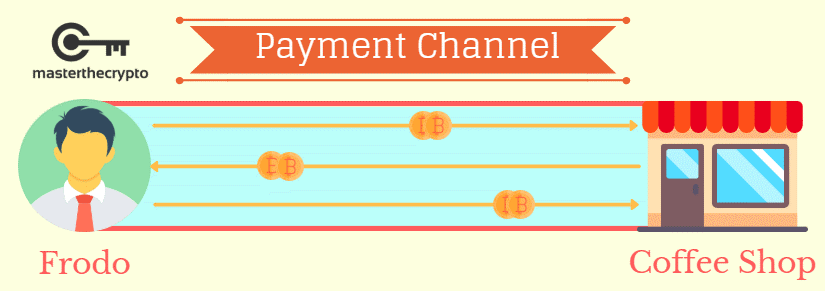
Another type of off-chain solutions is state channels, which is similar in concept to sidechains. A state channel is an approach where one completely re-imagines the idea of trustless consensus between two parties. Instead of coming up with a global consensus on a public network, we can use local consensus. In order to take advantage of state channels, one must create a payment channel with a node that’s connected to a larger network. Security in state channels is usually achieved by locking up some tokens on the main network and keeping them as collateral to ensure honest behavior. Here is an example of a payment channel:
Let’s look at the different implementations of layer 2 solutions out there.
1) Plasma
Plasma is the sidechain implementation for Ethereum Blockchain which is leverages on smart contracts that takes care of all the rules and validation/governance on the Plasma chain.
Block validation on the sidechain is either done by a single operator or by a consensus of a much smaller set of validators than that of the base layer. This alone allows for the quickening of block frequency and the number of maximum possible transactions in each block. Moreover, this will avoid the issue of block propagation and latency which is always the case for base-layer blockchains, where the block must be accepted by tens of thousands of nodes around the world.
The main drawback and problem with this approach is that sidechains always introduce some degree of centralization. Ethereum developers are constantly innovating and pushing the boundaries to preserve the principle of decentralization and trustlessness as much as possible. The gateway that transfers Ether (ETH) or Bitcoin (BTC) is usually controlled by a single party and can be vulnerable to various attacks. Even though the chain operators cannot necessarily steal user funds due to the protocol rules, they still can acquire transaction data, deanonymize users or withhold some information.
(Read also: Analyzing Cryptocurrency Risk: Existing Coins vs ICO)
2) Lightning Network
Lightning Network is probably the most well-known second layer payment network which is built for Bitcoin and Bitcoin-like blockchains (e.g. Decred, Litecoin). The idea of having a peer-to-peer network that consists of payment channels is almost as old as Bitcoin itself. Satoshi Nakamoto mentioned this approach in his comments on a BitcoinTalk forum back in 2010. The Lightning Network utilizes the concept of payment channels to provide bi-directional monetary transfers and envisions a network with near-instantaneous speed, zero counterparty risk, and low fees.
The main concept in LN is a payment channel that can be opened among any two users by including a special funding transaction in the underlying blockchain. Such a transaction is completed in a form of 2-of-2 multi-sig, meaning no party can single-handedly withdraw the money. In ensuring that funds won’t be lost forever in the channel in the case of non-cooperation, or if the private key is lost, both sides are required to sign each other’s transactions to execute the transaction.
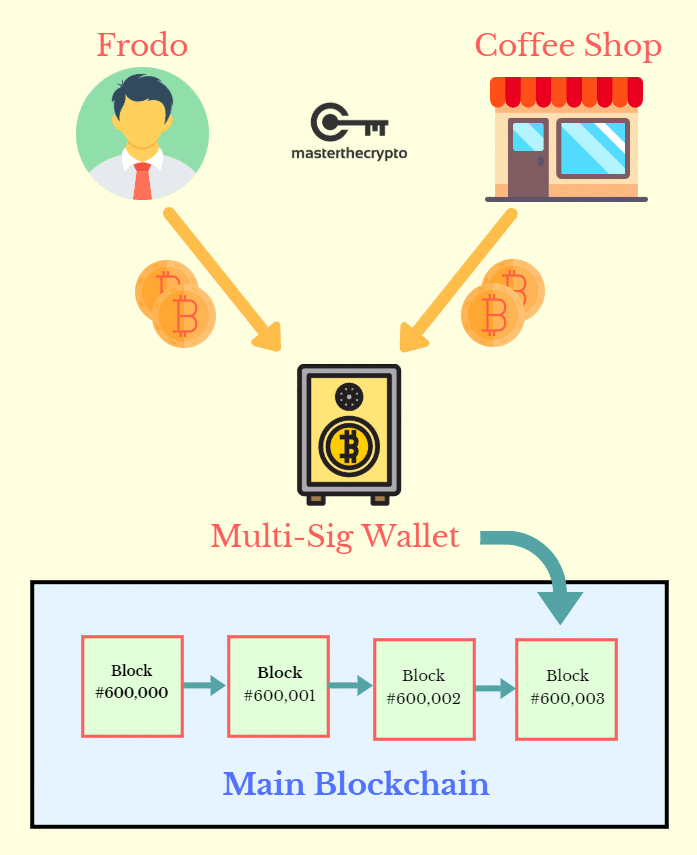
Once the channel is open and funded with some BTC, both parties can transact as fast as their peer-to-peer connection allows and pay no fees for doing so. Lightning transactions are completed in the form of cryptographic commitments. This allows for completely trustless payments; any party can close the channel and fix the outstanding trading balance on the Bitcoin blockchain at any time. In addition, LN ensures that it is impossible to cheat your trading partner by publishing an outdated commitment. This is done by having some lockup time on funds in the multi-sig. If Alice sees that Bob tries to cheat her by publishing some outdated state of their trading history (the one that is beneficial for him), she can simply provide proof in a form of a later commitment and free her funds from the multi-sig. Bob, in turn, will be punished for cheating by the protocol rules. It is the same general approach that Plasma uses to proof honesty on Plasma chain operators, though it is implemented in a different manner.
In most cases, both parties have an incentive to collaborate. In this case, the channel is closed with full cooperation of both parties by constructing a normal transaction from the original 2-of-2 escrow. This transaction would pay out the respective balance to each member, based on the most recent commitments. Neither individual has to go through the slow process of paying additional on-chain fees, nor lose out on the opportunity costs of having their BTC locked up by the protocol.
The practical use-case of LN is not that every single user will publish an onchain transaction whenever they need to make a payment; rather it will work as an actual network. If Alice does not have a direct channel opened with Bob, she can always create a multi-hop transaction that will use several channels to reach its destination – pretty much the way internet works.
Another benefit of LN is that it’s not controlled by any corporation or even a group of developers. The development started with writing a documentation called BOLT (Basis of the Lightning Technology). These BOLTs describe every aspect of the protocol in forensic detail using pseudocode and plain English. There are multiple teams around the world building an actual implementation of Lightning Network using different programming languages and platforms, but since they all collaborate on the same reference specification, the resulting software is interoperable.
The beautiful thing is that actions required to make or receive payment in Bitcoin via Lightning Network rarely takes place on-chain. This saves tremendous costs and speeds up trading significantly.
(See more: Guide to Bitcoin Scalability Solution: What is Lightning Network?)
3) GEO Protocol
GEO protocol is an off-chain scaling solution that can be built on top of any existing public blockchain and connect them in a single cross-chain network. There is no common ledger that requires computationally-expensive nodes and power to secure. Instead, it is an off-chain protocol that leverages on a distributed network of state channels and trustlines connecting them. The advantage is that unlike Bitcoin, Ethereum or Plasma, a GEO node can be spun up on a comparably slow and cheap device – like a smartphone or Raspberry Pi computer.
GEO is leveraging the concept of trustlines which was pioneered by Ryan Fugger from Ripple. The idea is quite similar to bidirectional channels in LN or Raiden, but the main difference being that trustlines occur when there is a bilateral agreement between exactly two users. This agreement consists of two credit lines (liabilities), as well as a balance indicating if, and how much, one party owes the other. Payments between non-trusting strangers are implemented by propagating balance updates through a network of trustlines until the payment reaches the receiver.
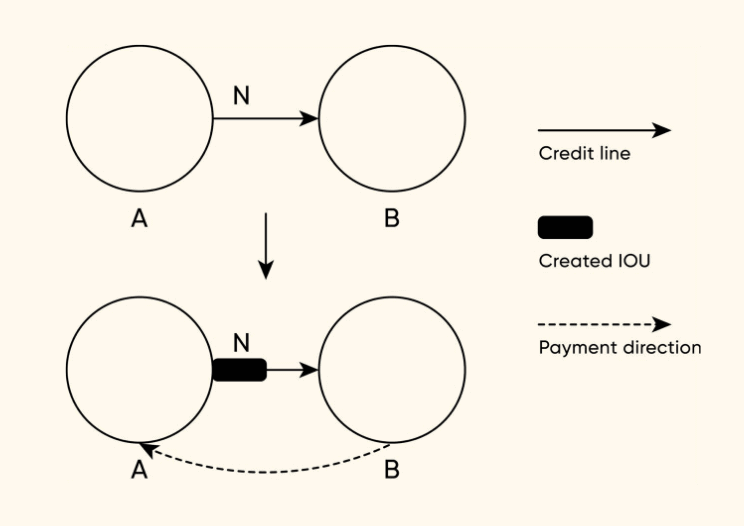
Trustlines mechanics
Trustlines consist of IOU (I Owe You) channels where users can issue their own currency or asset and the network facilitates free and unrestricted exchange of that asset. This also allows cross-blockchain exchange of value directly between holders without engaging with centralized exchanges. In order to preserve the decentralized and trustless nature of blockchain technology, the protocol does not allow freezing of either account or trustline.
Another concept developed by GEO protocol is composite channels, which are a combination of trustlines with user-issued assets and classic state channels with cryptocurrency locked up in an on-chain multisig wallet. This combines almost infinite scalability with a trustlessness of the base layer blockchain or multiple blockchains. At the end of the day, the user is allowed to not only make cryptocurrency transactions, but also tokenized fiat money, real world property and other assets. One tangible example of this technology would be a cross-chain DEx (decentralized exchange) enabled by the protocol from scratch.
4) Celer Network
Celer Network is a blockchain agnostic and horizontally scalable protocol that increases the scalability of blockchains through off-chain scaling. It utilizes a layered technology architecture, with several core technical innovations including:
- Channel construct suite with sidechain channels and flexible support for generalized off-chain dApp state transitions
- Optimal state routing algorithm with 15x higher transaction throughput than existing state-of-the-art solutions
- Off-chain operating system that simplifies development and usage of off-chain applications on various platforms
It should be noted that there are other solutions that have taken a similar approach such as the Lightning Network, Raiden, Trinity and Plasma. Celer Network differentiates itself because it will be compatible with all the other projects fighting to scale on-chain. This is important to consider because other projects in this space such as the Lightning Network (LN) cannot work with ETH or EOS.
(Read also: Guide to Crypto Derivatives: What is Cryptocurrency Derivatives?)
5) Raiden Network
Just like Lightning Network for Bitcoin, Raiden creates a sequence of payment channels outside of the blockchain itself to resolve transactions quickly. Raiden, however, has its own ERC20-based token called RDN which is not required to make payments but will be used to get access to additional services. At some point, the team has raised $33 million to fund the development of the project via an ICO – initial coin offering.
One of the first implementations of Raiden Network is called µRaiden, which is specifically designed for micro payments in ERC20-based tokens. The difference is that µRaiden only uses unidirectional payment channels, whereas Lightning Network is leveraging bidirectional payment channels.
What Does the Future Hold?
It is imperative that blockchains radically enhance their scaling capabilities to support higher transaction output and allow for mass adoption. Solving the issue of scalability is being rigorously undertaken by the cryptocurrency community, as can be seen from the above examples. It is only a matter of time before different variations of blockchains are able to preserve the principles of decentralization as well as possessing the scaling capabilities similar to traditional payment processes such as Visa or Mastercard. Second layer networks will extend the capacity of blockchain technology and open new use-cases that in turn will bring Ethereum, Bitcoin and other technologies into the hands of the next billion people.
(You might also be interested in: Crypto ICO vs. Stock IPO: What’s the Difference?)
Beneficial Resources To Get You Started
If you're starting your journey into the complex world of cryptocurrencies, here's a list of useful resources and guides that will get you on your way:
Trading & Exchange
- Crypto Guide 101: Choosing The Best Cryptocurrency Exchange
- Guide to Bittrex Exchange: How to Trade on Bittrex
- Guide to Binance Exchange: How to Open Binance Account and What You Should Know
- Guide to Etherdelta Exchange: How to Trade on Etherdelta
- Guide To Cryptocurrency Trading Basics: Introduction to Crypto Technical Analysis
- Cryptocurrency Trading: Understanding Cryptocurrency Trading Pairs & How it Works
- Crypto Trading Guide: 4 Common Pitfalls Every Crypto Trader Will Experience
Wallets
- Guide to Cryptocurrency Wallets: Why Do You Need Wallets?
- Guide to Cryptocurrency Wallets: Opening a Bitcoin Wallet
- Guide to Cryptocurrency Wallets: Opening a MyEtherWallet (MEW)
Read also: Crypto Trading Guide: 4 Common Pitfalls Every Crypto Trader Will Experience and Guide To Cryptocurrency Trading Basics: Introduction to Crypto Technical Analysis.
Get our exclusive e-book which will guide you on the step-by-step process to get started with making money via Cryptocurrency investments!
You can also join our Facebook group at Master The Crypto: Advanced Cryptocurrency Knowledge to ask any questions regarding cryptos!

